The Attack
Marcus Hutchins, a computer security researcher from the UK, was just 22 years old when he discovered the kill-switch for WannaCry, a malware infection that quickly took over the globe. When it hit in 2017, WannaCry was one of the fastest-spreading computer worms the world had seen. The National Health Service, the UK’s largest publicly-funded healthcare system, was the first target hit by the worm. Human lives were at stake, with one third of NHS hospital trusts infected and 19,494 patient appointments canceled as a result. In short time, the malware had spread to a multitude of other industries around the globe, causing damages estimated between $4 billion and $8 billion.
WannaCry was a form of ransomware, malicious software designed to block access until a sum of money is paid. It was able to spread easily from machine to machine using a piece of code called EternalBlue. This code originated with the NSA and was stolen and leaked by a group of hackers known as the “Shadow Brokers.” The code exploited outdated versions of Windows machines, which are commonly found in the healthcare system.
On the day that WannaCry hit in May of 2017, Marcus gained access to the malware’s code and quickly began testing it in his quarantined environment. Inside the code, he found a request being made to an unregistered website, so he registered the obscure domain. This was a type of built in “kill-switch,” something normally designed by the creator as a safeguard from backfire. Sure enough, after Marcus had registered that website, reported cases of WannaCry began to decline, but Marcus knew there was still a risk of the domain being attacked and brought down. He worked for weeks to communicate with victims and actively protect the domain he had registered while it was being pummeled with useless traffic (an attack known as distributed denial of service, or DDoS). Marcus received help from cybersecurity firm Kryptos Logic and DDoS mitigation firm Cloudflare to protect the domain. After weeks of mitigation and very little sleep, Marcus could finally celebrate his accomplishments. This incident had made international headlines, and the media quickly identified Marcus as the person behind his online alias MalwareTech. Though a bit uncomfortable with this overnight fame, he came to appreciate the support. Later that summer he celebrated with friends at DEF CON, the famous annual hacker conference that takes place in Las Vegas, NV. It was at the end of this trip when Marcus would encounter the toughest period of his life.
A Dark Past
Before Marcus’s real name was discovered from his heroic efforts, he was known by the online alias “MalwareTech.” Under this handle he published vulnerability research and reverse-engineering security blog posts, and used Twitter to communicate to followers and tech enthusiasts. At age 17 he became involved in cyber-criminal affairs, most notably with development of the banking malware “Kronos.” This malware was sold to multiple “black-hat” (malicious) hacking groups and used to obtain sensitive personal information from users’ online banking activity. According to his interview with Wired, Marcus’s perception of his own moral code was shifting the more he communicated with colleagues in the dark web. The better he got at developing his own malware, the more reputable he became in these communities, and the tougher it became to turn down monetary offers in exchange for his code. When he initially refused to develop the banking trojan, he was threatened to be exposed to the FBI by the requester. He contributed to the development of Kronos in 2014, and his exposure from WannaCry would later uncover his past mistakes.
Vegas, 2017
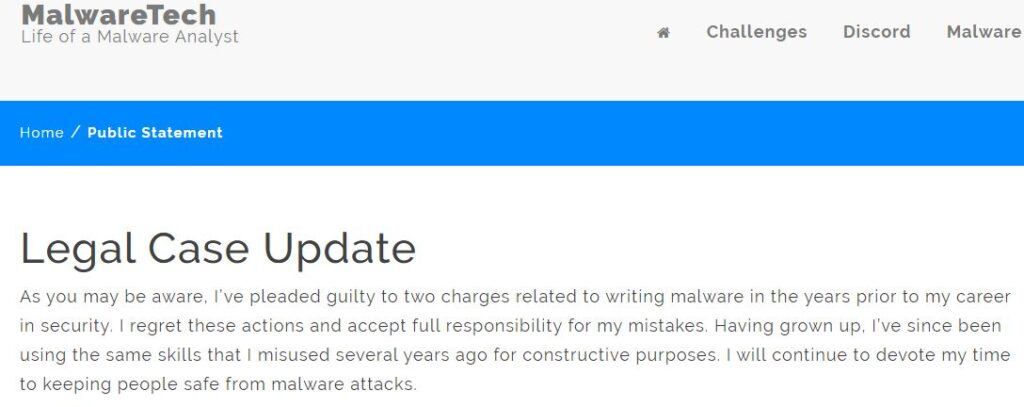
His real identity now public as a result of his fame, the FBI eventually caught up with Marcus. He was interrogated at McCarran Airport after a week of partying at the hacker convention in Vegas. Charged with creation of the Kronos malware, he was jailed, but the online community of supporters quickly came to his aid and posted a $30,000 bond. He was relocated permanently to the U.S. and placed on house arrest until further notice, while his lawyers began chipping away at the terms of his detainment. In July of 2019, Marcus was set to have his sentence hearing in Milwaukee. He had pleaded guilty to charges two months prior and released a short public statement approved by attorneys, shown below:
Fair Judgment
“In my career I’ve found few people are truly evil, most are just too far disconnected from the effects of their actions…until someone reconnects them.” ~Hutchins
The judge assigned to Marcus’s case took a broad view of his life, noting that Marcus had “turned the corner” from his earlier conduct. The judge recognized that Marcus would be a valuable asset in protecting society from future malicious cyber attacks. Marcus was sentenced only to “time served, with a one year period of supervised release.” His visa had expired, and Marcus spent his last year in the U.S. hoping to get back to work, and “to put the weight of all those feats and secrets, on both sides of the moral scale, behind him.” This is Marcus’s story of reckoning. He remains pained by his past responsibility for malice, but his story sheds a new light for the hacker community; one that might guide their purpose toward making the world a better place.
To read more:
https://www.wired.com/story/confessions-marcus-hutchins-hacker-who-saved-the-internet/